Documentation Index
Fetch the complete documentation index at: https://docs.streamnative.io/llms.txt
Use this file to discover all available pages before exploring further.
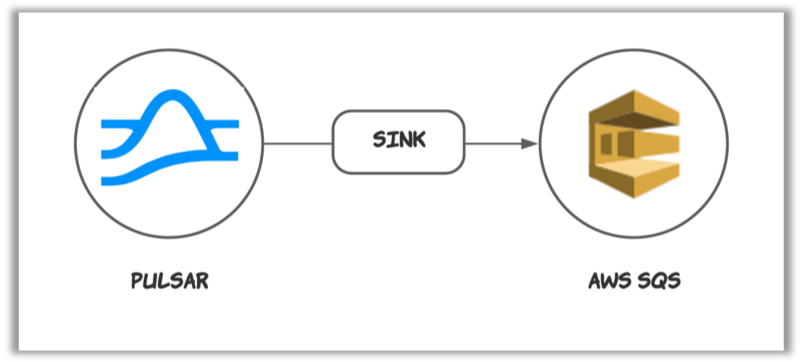
This connector is available as a built-in connector on StreamNative Cloud.
Quick start
Prerequisites
The prerequisites for connecting an AWS SQS sink connector to external systems include:- Create SQS in AWS.
- Create the AWS User and create
AccessKey(Please recordAccessKeyandSecretAccessKey). - Assign the following permissions to the AWS User:
- sqs:CreateQueue
- sqs:SendMessage
1. Create a connector
The following command shows how to use pulsarctl to create abuiltin connector. If you want to create a non-builtin connector,
you need to replace --sink-type sqs with --archive /path/to/pulsar-io-sqs.nar. You can find the button to download the nar package at the beginning of the document.
If you are a StreamNative Cloud user, you need set up your environment first.
--sink-config is the minimum necessary configuration for starting this connector, and it is a JSON string. You need to substitute the relevant parameters with your own.
If you want to configure more parameters, see Configuration Properties for reference.
You can also choose to use a variety of other tools to create a connector:
- pulsar-admin: The command arguments for
pulsar-adminare similar to those ofpulsarctl. You can find an example for StreamNative Cloud Doc. - RestAPI: You can find an example for StreamNative Cloud Doc.
- Terraform: You can find an example for StreamNative Cloud Doc.
- Function Mesh: The docker image can be found at the beginning of the document.
2. Send messages to the topic
If your connector is created on StreamNative Cloud, you need to authenticate your clients. See Build applications using Pulsar clients for more information.
3. Show data on AWS SQS
You can use the following simple code to receive messages from AWS SQS.Configuration Properties
Before using the AWS SQS sink connector, you need to configure it. This table outlines the properties and the Descriptions of an AWS SQS sink connector.| Name | Type | Required | Sensitive | Default | Description |
|---|---|---|---|---|---|
awsRegion | String | true | false | ” ” (empty string) | Supported AWS region. For example, us-west-1, us-west-2. |
queueName | String | true | false | ” ” (empty string) | The name of the SQS queue that messages should be read from or written to. |
awsCredentialPluginName | String | false | false | ” ” (empty string) | The fully-qualified class name of implementation of AwsCredentialProviderPlugin. For more information, see [Configure AwsCredentialProviderPlugin](###Configure AwsCredentialProviderPlugin). |
awsCredentialPluginParam | String | false | true | ” ” (empty string) | The JSON parameter to initialize awsCredentialsProviderPlugin. For more information, see [Configure AwsCredentialProviderPlugin](###Configure AwsCredentialProviderPlugin). |
awsEndpoint | String | false | false | ” ” (empty string) | AWS SQS end-point URL. You can find it at AWS SQS Service endpoints. |
fifoMessageGroupIdSource | String | false | false | topicPartitionName | Source for MessageGroupId when FIFO is enabled. Supported: topicPartitionName, messageKey. FIFO is detected automatically when queueName ends with .fifo. |
metadataFields | String | false | false | ”pulsar.key” | The metadata fields to be sent to the SQS message attributes. Valid values are ‘pulsar.topic, pulsar.key, pulsar.partitionIndex, pulsar.sequence, pulsar.properties.{{Your properties key}}, pulsar.eventTime’ |
Configure AwsCredentialProviderPlugin
AWS SQS sink connector allows you to use three ways to connect to AWS SQS by configuringawsCredentialPluginName.
-
Leave
awsCredentialPluginNameempty to get the connector authenticated by passingaccessKeyandsecretKeyinawsCredentialPluginParam. -
Set
awsCredentialPluginNametoorg.apache.pulsar.io.aws.AwsDefaultProviderChainPluginto use the default AWS provider chain. With this option, you don’t need to configureawsCredentialPluginParam. For more information, see AWS documentation. -
Set
awsCredentialPluginNametoorg.apache.pulsar.io.aws.STSAssumeRoleProviderPluginto use the default AWS provider chain, and you need to configureroleArnandroleSessionNmaeinawsCredentialPluginParam. For more information, see AWS documentation.
Advanced features
Schema Support
The AWS SQS sink connector supports the following schema types:Primitive Schema, Avro Schema, and JSON Schema.
Primitive Schema
For the primitive type, the payload format is as follows:| Primitive Schema Type | JSON Conversion Type | Example |
|---|---|---|
| Boolean | Boolean | true |
| INT8, INT16, INT32, INT64, FLOAT, DOUBLE | Number | 1234 |
| STRING | String | ”Hello” |
| BYTES | Base64-encoded String | ”SGVsbG8=” (base64-encoded version of the string “Hello”) |
| DATE, TIME, TIMESTAMP | ISO 8601 String (yyy-MM-dd’T’HH:mm:ss.SSSXXX) | ‘2023-10-30T06:13:48.123+08:00’ |
| LocalDate | ISO 8601 String (yyyy-MM-dd) | ‘2023-10-17’ |
| LocalTime | ISO 8601 String (HH:mm:ss.SSSSSSSSS) | ‘04:30:33.123456789’ |
| LocalDateTime | ISO 8601 String (yyyy-MM-dd’T’HH:mm:ss.SSSSSSSSS) | ‘2023-10-17T04:30:33.123456789’ |
| Instant | ISO 8601 String (yyyy-MM-dd’T’HH:mm:ss.SSSSSSSSSXXX) | ‘2023-10-30T06:13:48.123456789+08:00’ |
Struct Schema (Avro Schema and JSON Schema)
For the struct schema typesJSON and AVRO, the value is converted into a JSON object. The conversion rules outlined
in the Primitive schema section are applied to all primitive type fields within this value object. Nested objects are
also supported.
Here is an example:
AVRO and JSON):
| Logical Type | JSON Conversion Type | Example |
|---|---|---|
time-millis, time-micros | ISO 8601 String (HH:mm:ss.SSS) | ‘13:48:41.123’ |
timestamp-millis | ISO 8601 String (yyy-MM-dd’T’HH:mm:ss.SSSXXX) | ‘2023-10-30T06:13:48.123+08:00’ |
timestamp-micros | ISO 8601 String (yyy-MM-dd’T’HH:mm:ss.SSSSSSXXX) | ‘2023-10-30T06:13:48.123456+08:00’ |
local-timestamp-millis | ISO 8601 String (yyyy-MM-dd’T’HH:mm:ss.SSS) | ‘2023-10-29T22:13:48.123’ |
local-timestamp-micros | ISO 8601 String (yyyy-MM-dd’T’HH:mm:ss.SSSSSS) | ‘2023-10-29T22:13:48.123456’ |
Metadata Support
SQS sink connector will put metadata of Pulsar into SQSmessage attributes. SQS message attributes accommodate various data types such as String, Number, Binary, and so forth.
The supported metadata fields of Pulsar are:
topic: Thestringtype of source topic namekey: Thestringtype of the message key.partitionIndex: Thenumbertype of the topic partition index of the topic.sequence: Thenumbertype of the sequence ID.properties: This is a map, and will unfold this map, placing each key-value pair into the SQSmessage attribute. The type of the key isstring, and the type of the value isstring.eventTime: The event time of the message in the ISO 8601 formatmessageId: The string representation of a message ID. eg,"1:1:-1:-1"
message attributes, for examples:
metaDataField configuration. It is a string in which multiple fields are separated by commas. And this connector will verify that the number of metadata cannot exceed 10.
For examples:
FIFO Support
Note: Enabling FIFO mode will lower the sink’s throughput in exchange for strict ordering guarantees- Detection: When
queueNameends with.fifo, the connector treats the queue as FIFO. - MessageGroupId: Controlled by
fifoMessageGroupIdSource.topicPartitionName(default): Uses full Pulsar topic name (including-partition-x) to preserve per-partition order.messageKey: Uses Pulsarkey, suitable for non-partitioned topics requiring key-based ordering.
- MessageDeduplicationId: Always uses Pulsar
messageId. - Standard queues: If not FIFO, the connector does not set FIFO-specific fields.